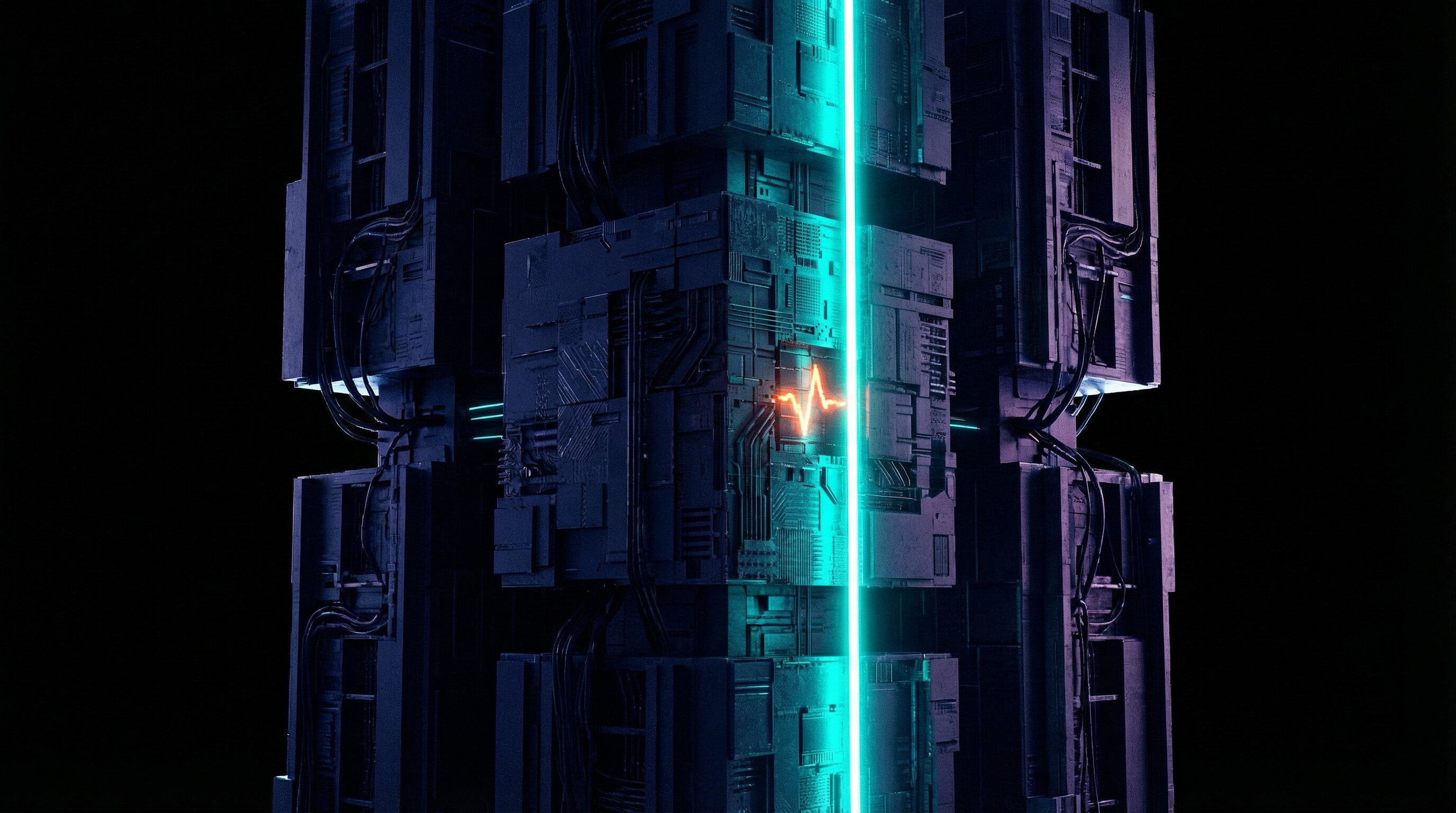
FIND THE BREACH
THAT OTHERS HAVE MISSED
The next nine-figure data breach is already hiding in your log archives.DEFENDRA™ AI finds latent threats before they can cripple your business.
INTEGRATES WITH VARIOUS DATA LAKES:
EXTEND YOUR CURRENT SIEM ENVIRONMENT
We use open standards that work with any data lake and ensure your log data is always accessible.
Improved Threat Detection
Add auxiliary logs to your SOC’s overall log analysis process to complement your Splunk (or other SIEM) deployment. Improve threat investigations with enhanced analytics and anomaly detection by examining the overall infrastructure combining the Splunk data and auxiliary logs to uncover previously unseen threats.
Cold Data Analytics
SIEMs are designed for real-time monitoring, not deep analysis of cold data. “PROJECT DEFENDRA”, with its standards based approach, delivers cost-effective long-term storage of cold logs in the lakehouse of your choice. This enables analysis for “slow and low” threats as well as newly identified attack techniques that can be searched for in the cold logs.
Open Standards
By using a standards based approach, “PROJECT DEFENDRA” provides safety in security. Any lakehouse can be used for the long-term storage of log data and indexes. This minimizes storage costs while ensuring the data is available for access by a wide variety of tools and technologies. The analytics and AI-driven anomaly detection from “PROJECT DEFENDRA” can be used, plus organizations can add their own analytic searches to further extend the solution.
PROACTIVE DEFENSE.
PROFITABLE ECONOMICS.
DEFENDRA™ AI is the only platform that makes continuous, deep archival scanning economically feasible, neutralizing threats before they become headlines.
DEFEND
Analyze logs that slip through the cracks. Most SIEM platforms only ingest a fraction of available log data due to cost and performance constraints. We store and examine the rest of the log data (auxiliary logs) that your SIEM does not. We expand your security visibility by performing analytics and anomaly detection across the SIEM logs and auxiliary logs.
- Supports any Data Lake
- Provides visibility across the infrastructure
- Finds threats that would have been missed
DETECT
Unlock your log history. Threats don't always announce themselves immediately; many lie dormant for months or years. By storing the SIEM logs long-term as well as the auxiliary logs, analysis can be done as new threats are identified to find the early tell tale signs of an attack. Organizations often have to search these logs, but have limited access to them.
- Long-term cold log storage
- Check for updated attack techniques in cold logs
- Meet compliance obligations
DELIVER
"PROJECT DEFENDRA" provides cost-efficient storage techniques and faster analysis. Log data can be stored for years in an open format so that it will always be accessible. Keeping the logs indexed ensures that analysis can be performed quickly when it is needed for analyzing new attack techniques, meeting compliance requirements, or responding to an attack.
- Up to 9x data reduction
- Logs and indexes stay together
- Works on any storage tier
DON'T WAIT FOR THE BREACH. PREVENT IT.
Request a confidential, no-obligation Archival Threat Assessment. The DEFENDRA™ AI experts will map your potential blind spots and deliver a Breach Prevention ROI analysis.